Privileged Account Management
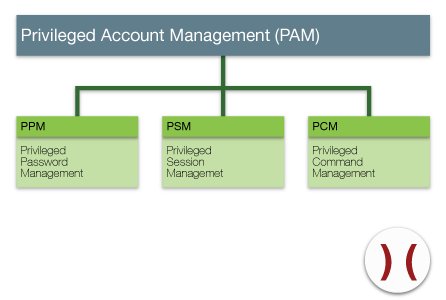
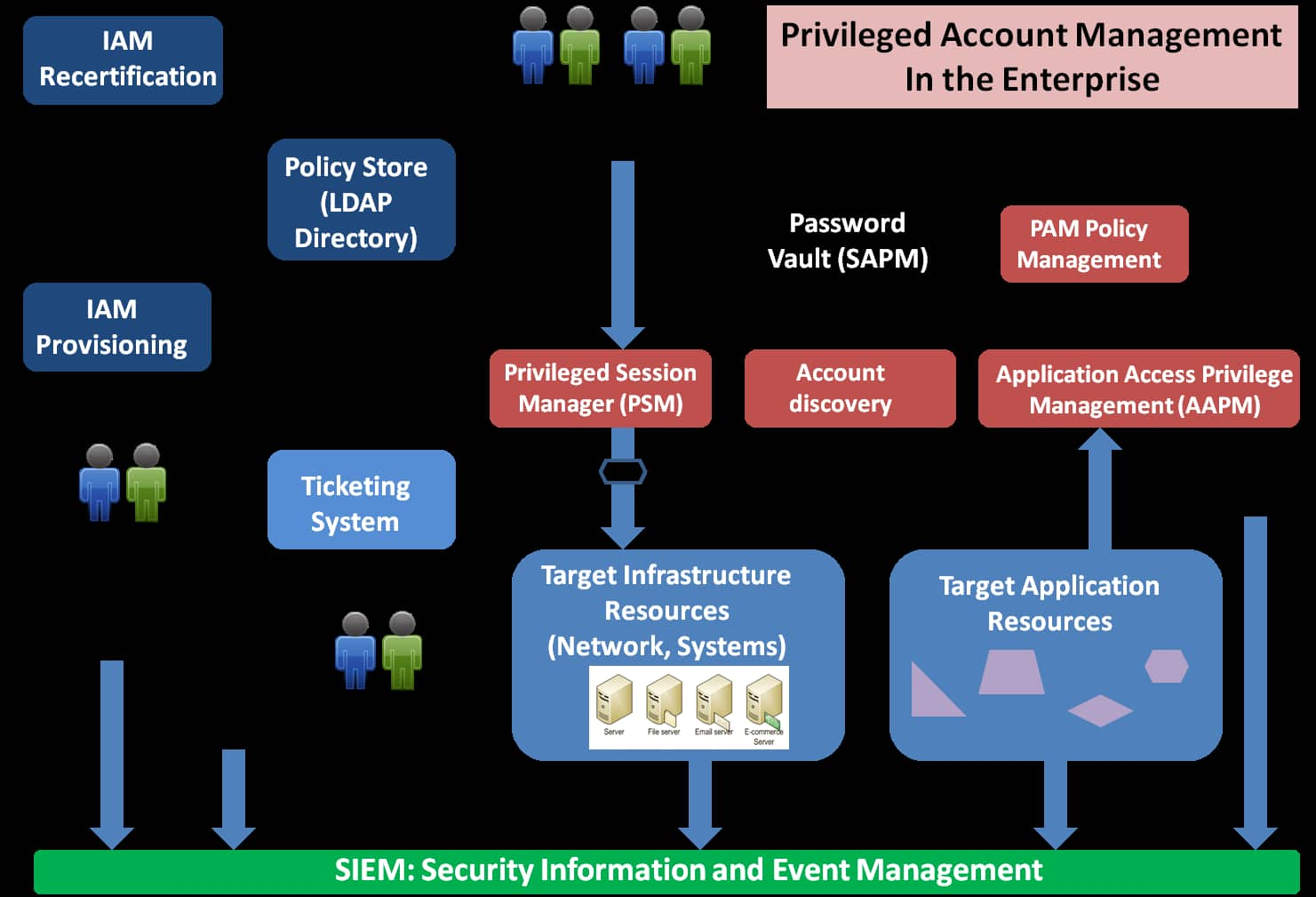
Privileged Account Management (PAM) is a domain within Identity and Access Management (IdAM) focusing on monitoring and controlling the use of privileged accounts Privileged accounts include local and domain administrative accounts, emergency accounts, application management, and service accounts These powerful accounts provide elevated, often nonrestricted access to the underlying IT.

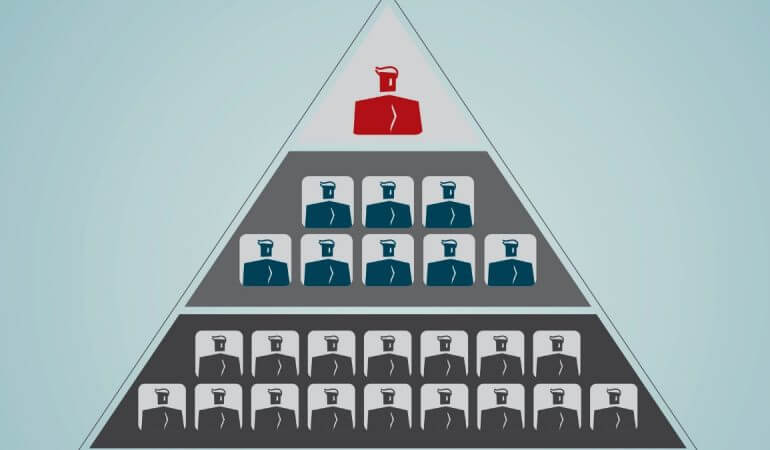
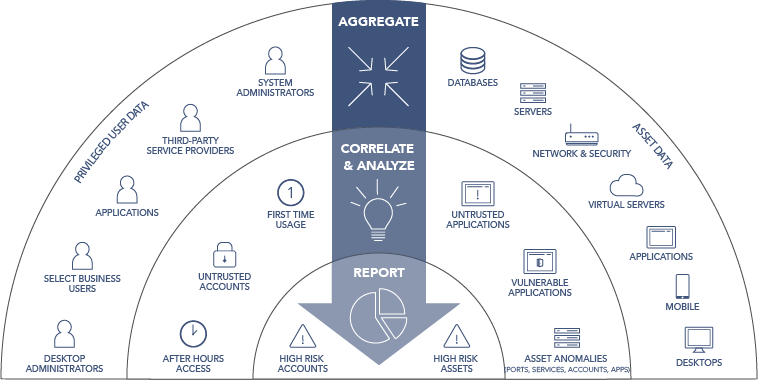
Privileged account management. BENEFITS OF PRIVILEGED ACCount MANAGEMENT ADVISORY Actionable insights based on the outcome of an analysis of the state of your environment and distribution of privileged accounts and their permissions;. Other privileged accounts which are often overlooked, but are just as vulnerable as the ones mentioned above, include service accounts, system accounts, application accounts, and SSH keys used by automated processes The modern approach to protecting these accounts is known as privileged access management or privileged access security (PAS). In this case, only their identity can unlock their personalised privileged accounts Implementing a RoleBased Account model In the rolebased account model, Applications, Systems and Devices have only the minimum number of Privileged Accounts needed to manage them For each role, an account with the minimum necessary privileges is created.
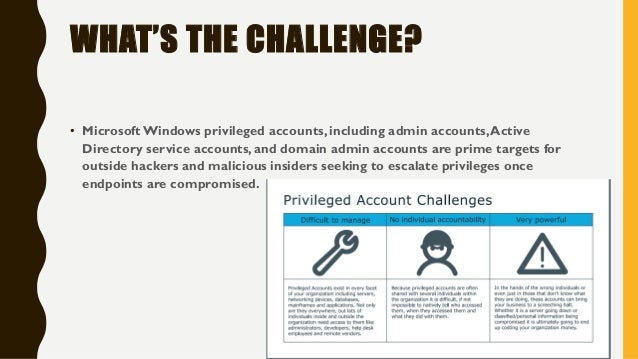
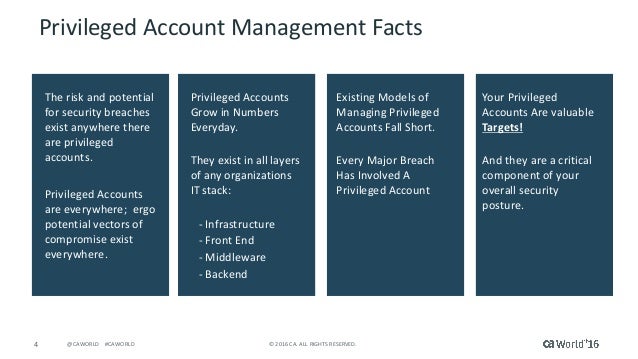
The term "privileged account" includes the most powerful accounts spread across an. Privileged account management (PAM) is emerging as one of the hottest topics in cybersecurity — and it’s easy to understand why Cybercriminals are relentless when it comes to finding and. Privileged Access Management Manual”, account review process and discuss any account structure that may need updates Team Members ICT directors/managers, Project Manager, and IT Compliance Officer Accounts IT departments may have a variation of accounts they track using the account inventory template, and to.
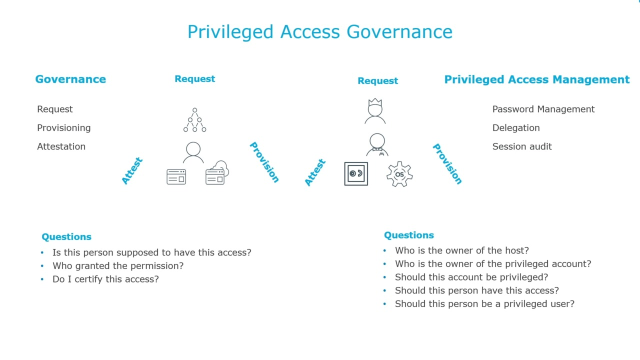
January 18, 21 January 18, 21 ARCON User IT security, Password Management, Privileged Access Management Irrespective of companies’ size and operation, protecting a highlevel admin account is an important element of an effective security strategy against cyberthreats. By combining the power of privileged account management (PAM) with identity governance, you’ll close security gaps, reduce risk and eliminate redundant processes for privileged and nonprivileged accounts Now you can streamlineIT using automated provisioning and deprovisioning, along with faster reporting and auditing for all your users. Values and stored in the privileged account management system The focus of this Privileged Password Security Policy document is on the second type of password, Privileged Account Passwords However, because User Account passwords often have elevated or administrative privileges attached to them, both types of passwords are.
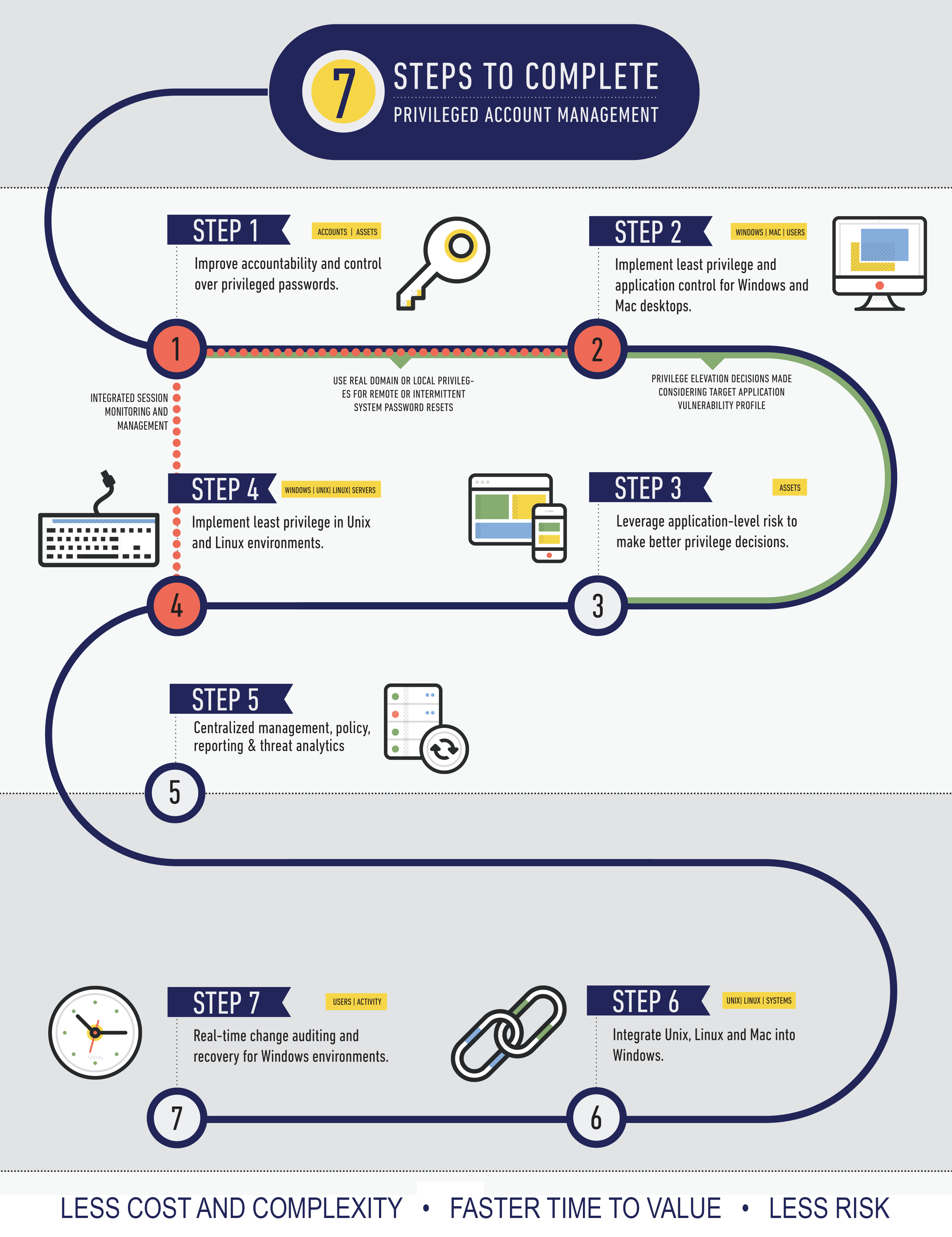
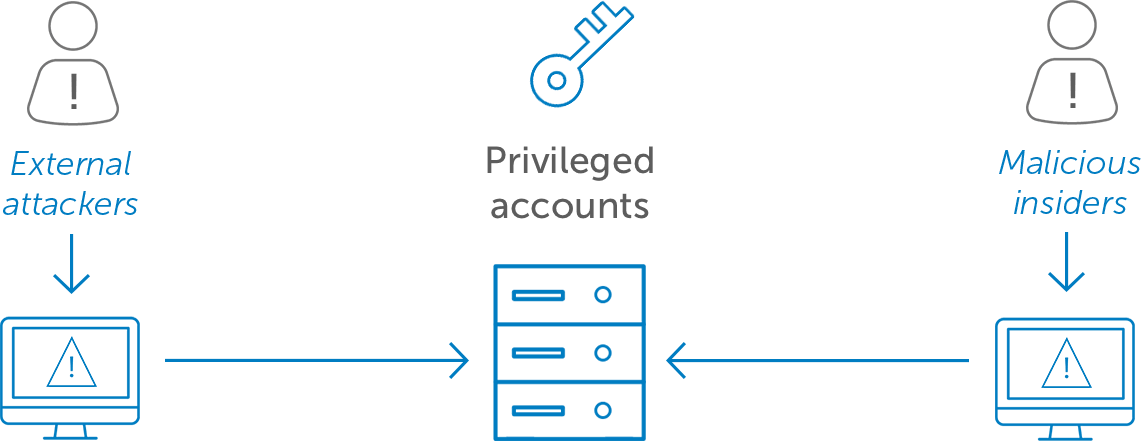
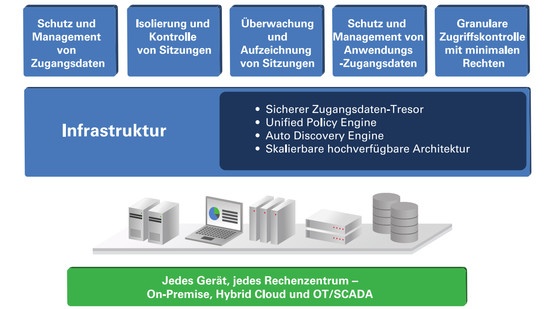
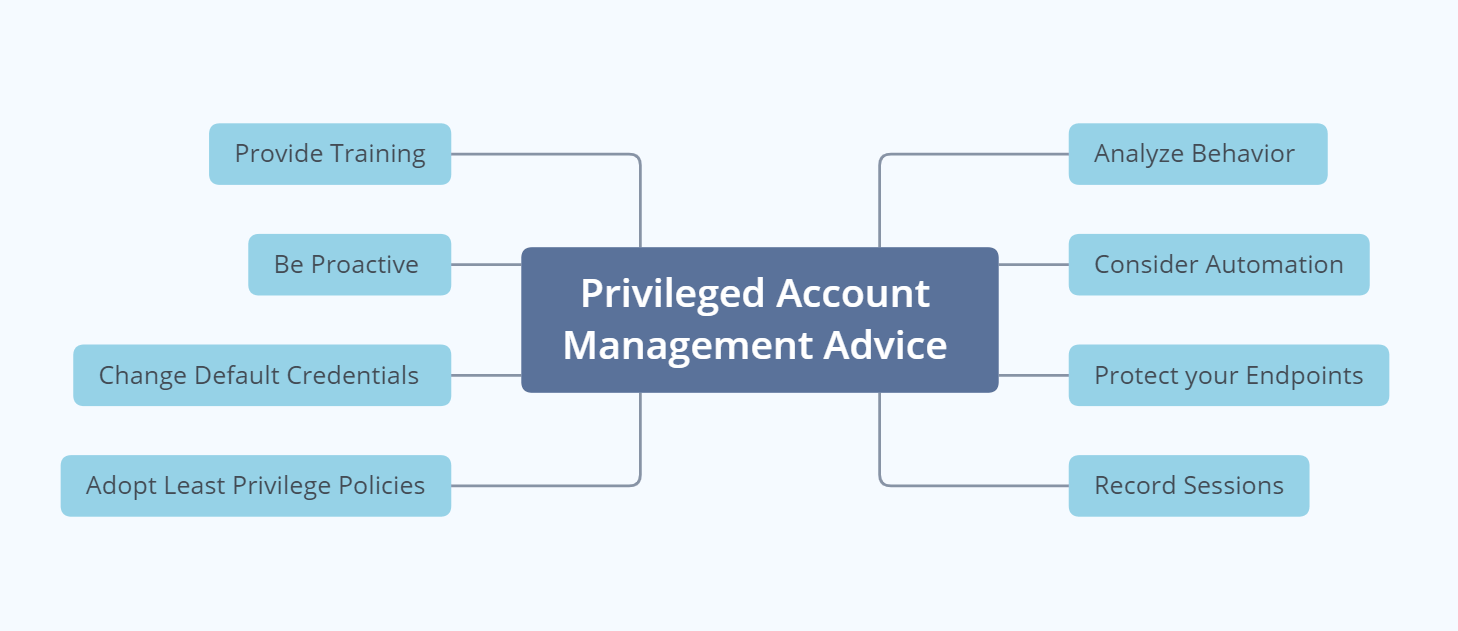
Privileged accounts are a necessity in any enterprise IT environment, since they enable administrators to manage the environment But as news reports constantly remind us, granting privileged access increases the risk of a security breach. Privileged Access Management (PAM) refers to systems that securely manage the accounts of users who have elevated permissions to critical, corporate resources These may be human administrators, devices, applications, and other types of users. Privileged Account Management and Security Best Practices As mentioned, privileged accounts must be protected better than standard accounts Privileged Account Management (PAM) essentially entails a rigid plan and IT infrastructure to manage all privileged accounts It entails a great deal of accounting, security, and monitoring.
Privileged Account Management and Privileged Identity Management (PIM) are similar There are also significant differences between them PAM manages privileged user access It allows exclusive access to core data and systems The PAM will block and isolate users in the network They can only access the areas they have the privilege to use. January 18, 21 January 18, 21 ARCON User IT security, Password Management, Privileged Access Management Irrespective of companies’ size and operation, protecting a highlevel admin account is an important element of an effective security strategy against cyberthreats. Privileged account management (PAM) is emerging as one of the hottest topics in cybersecurity — and it’s easy to understand why Cybercriminals are relentless when it comes to finding and.
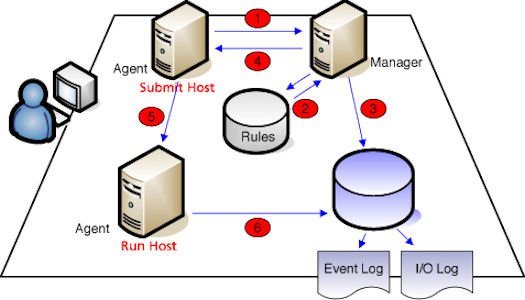
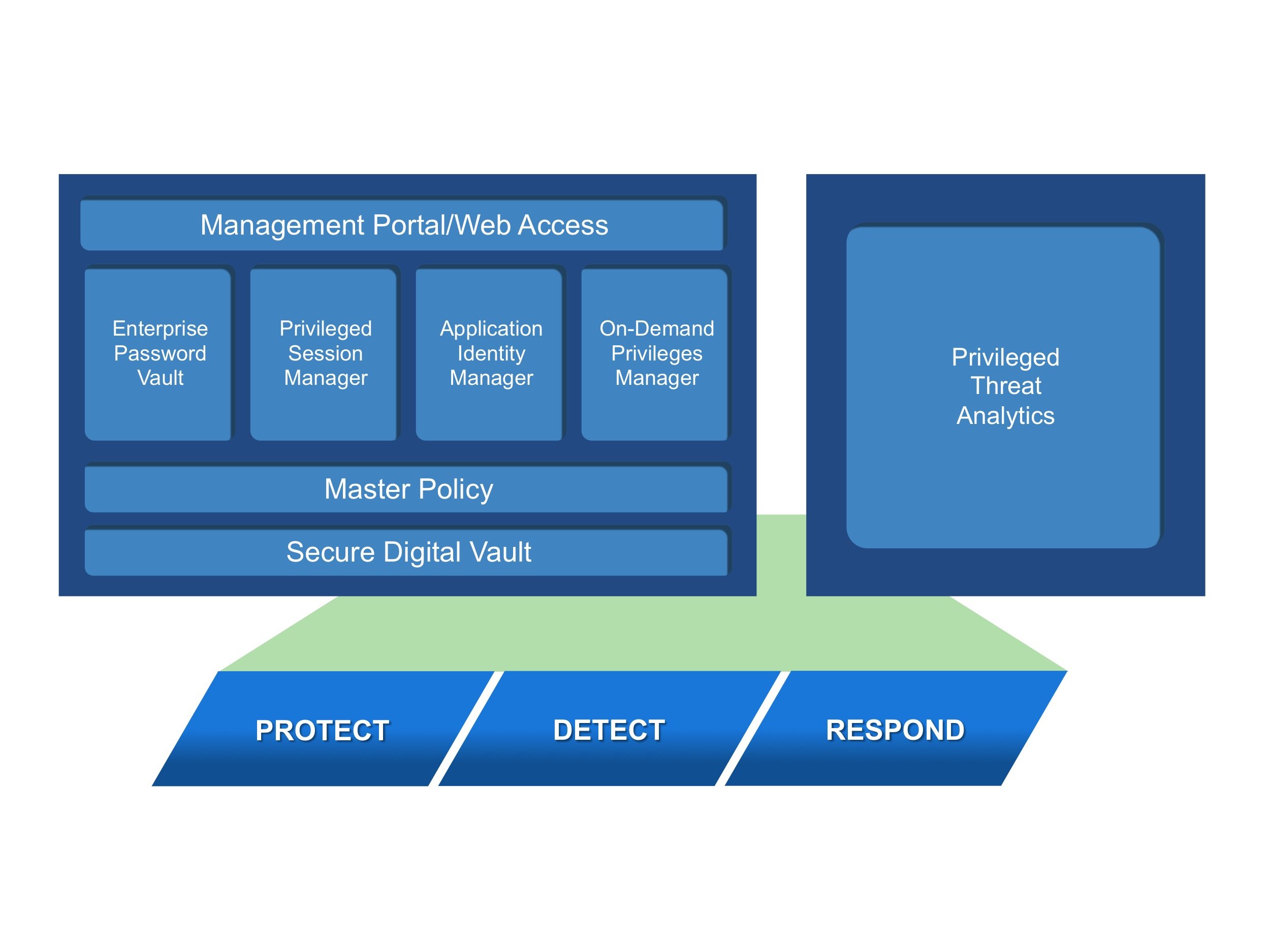
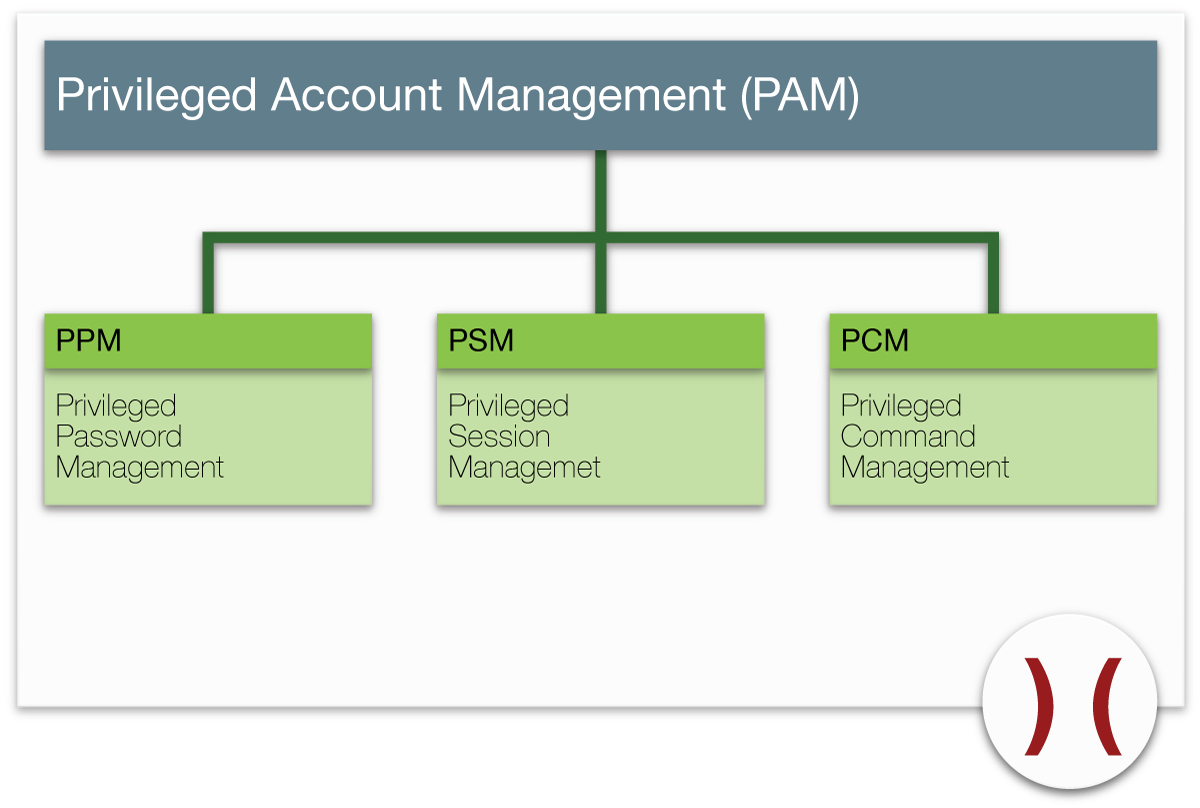
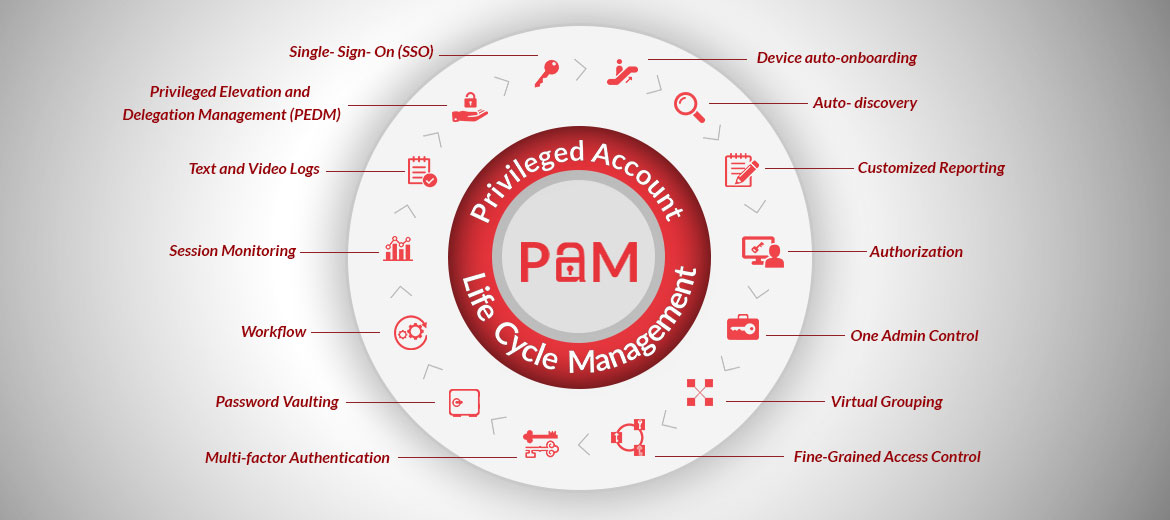
Privileged Account Management (PAM) 12/02/ Contributors Download PDF of this page Privileged Account Management (PAM) This feature provides a specific, auditable record of granular administrative permission sets granted to VDS and/or Active Directory privileged accounts External access automatically expires by default. This lab is intended to show the basic features of the CyberArk Privileged Access Security solution (CyberArk PAS) CyberArk PAS is one of the leading solutions in the Privileged Account Management (PAM) space, which is what WWT considers one of the five pillars of Identity and Access Management. Privileged password management systems can periodically audit password records, monitor for account login sessions, trigger alerts, write to logs, and shut down suspicious activity effortlessly A privileged password manager should be able to help you formulate a password policy and should also have the utility to implement those decisions.
Day after day, we see the evidence of an increased number of breaches As a Privileged Account Management (PAM) provider, we are also seeing a similar increase in requests for proposals on our Core Privileged Access Manager (BoKS) solution What is most interesting is that a large number of security professionals who contact us indicate that they are not not even sure what privileged accounts. Privileged Account Management and Security Best Practices As mentioned, privileged accounts must be protected better than standard accounts Privileged Account Management (PAM) essentially entails a rigid plan and IT infrastructure to manage all privileged accounts It entails a great deal of accounting, security, and monitoring. Privileged account management (PAM) is a domain within identity and access management (IdAM) that focuses on monitoring and controlling the use of privileged accounts Privileged accounts include local and domain administrative accounts, emergency accounts, application management, and service accounts These powerful accounts provide elevated, often nonrestricted, access to the underlying IT.
Privileged Account Management for Dummies is written for IT and systems administrators, along with security professionals responsible for protecting your organization from security threats It assumes a basic level of IT expertise and experience, but is also great for educating business users and others on the importance of privileged account. Privileged access security is something every organization needs to have in place as part of their fundamental security solutions The landscape of privileged account activity is constantly growing beyond the static corporate infrastructure (Cloud, DevOps, IoT, ) and so is. In this case, only their identity can unlock their personalised privileged accounts Implementing a RoleBased Account model In the rolebased account model, Applications, Systems and Devices have only the minimum number of Privileged Accounts needed to manage them For each role, an account with the minimum necessary privileges is created.
Examples of nonhuman privileged access Application account A privileged account that’s specific to the application software and is typically used to administer, configure or manage access to the application software Service account An account that an application or service uses to interact with the operating system Services use these. ARCON Privileged Access Management Overview The nature of cyberattacks is getting sophisticated in the everexpanding digital workplace For enterprise IT security teams, protecting privileged accounts, one of the major sources of data breaches, remains a top priority Cyber attacks ca. Privileged Account Management (PAM) refers to the process of maintaining and safeguarding the accounts within a system that have special access to sensitive data Privileged users can take a variety of forms, from trusted highsecurity company managers to IT contractors with the ability to access necessary data Delegating data management.
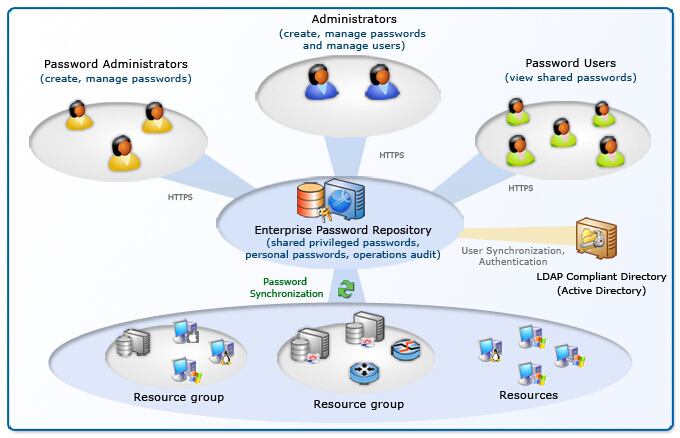
2 Simplify and Centralize Administration of Privileged Accounts Administration of privileged account management is also simplified A single point of administration allows business staff to request, approve, grant, and certify access to privileged accounts just as they do with other identityrelated activities. January 18, 21 January 18, 21 ARCON User IT security, Password Management, Privileged Access Management Irrespective of companies’ size and operation, protecting a highlevel admin account is an important element of an effective security strategy against cyberthreats. The Password Server itself is a fullfeatured shared account and password management solution It can be used in combination with Remote Desktop Manager for privileged account and session management tools integrating over 150 integrations and technologies Download this Directory and get our Free Privileged Access Management Buyer’s Guide.
By combining the power of privileged account management (PAM) with identity governance, you’ll close security gaps, reduce risk and eliminate redundant processes for privileged and nonprivileged accounts Now you can streamlineIT using automated provisioning and deprovisioning, along with faster reporting and auditing for all your users. Privileged Identity Management (PIM) is a service in Azure Active Directory (Azure AD) that enables you to manage, control, and monitor access to important resources in your organization These resources include resources in Azure AD, Azure, and other Microsoft Online Services such as Microsoft 365 or Microsoft Intune. The NCCoE recently released a draft of the NIST Special Publication (SP) Privileged Account Management for the Financial Services Sector The project's public comment period closed on November 30, 18 For ease of use, the guide is available to download or read in volumes SP A Executive Summary.
Leverage NetIQ Privileged Account Manager to provide the oversight and automation required to implement a comprehensive Zero Trust strategy Find the right balance between user productivity and keeping your most important assets, computers, databases, and applications safe Active session management identifies suspicious activity and allows for. Privileged Account Management The following parameters determine general account management settings MinValidityPeriod Description The number of minutes to wait from the last retrieval of the account until it is replaced This gives the user a minimum period to be able to use the password before it is replaced. By combining the power of privileged account management (PAM) with identity governance, you’ll close security gaps, reduce risk and eliminate redundant processes for privileged and nonprivileged accounts Now you can streamlineIT using automated provisioning and deprovisioning, along with faster reporting and auditing for all your users.
Privileged Account Management Recommendation Summary R 3 Define business practices and responsibilities for monitoring privileged accounts and implement privileged access management tools Additional Details Report Number ITAR Referenced Report Privileged Account Management. Privileged Account Management (PAM) With the increasing use of cloud computing and storage and interconnected Internet of Things, as well as the growing number of systems, remote users, and large volumes of data, today’s business environment and security risks have changed enormously and require a shift in our security mindset and practices. Realistic assessment of the state of your organization’s privileged access capabilities and identification of both high risk accounts and low hanging fruit for risk mitigation.
Privileged Account Management Recommendation Summary R 3 Define business practices and responsibilities for monitoring privileged accounts and implement privileged access management tools Additional Details Report Number ITAR Referenced Report Privileged Account Management. Privileged Access Management Manual”, account review process and discuss any account structure that may need updates Team Members ICT directors/managers, Project Manager, and IT Compliance Officer Accounts IT departments may have a variation of accounts they track using the account inventory template, and to. January 18, 21 January 18, 21 ARCON User IT security, Password Management, Privileged Access Management Irrespective of companies’ size and operation, protecting a highlevel admin account is an important element of an effective security strategy against cyberthreats.
The Privileged Account Management for the Financial Services Sector Report The National Cybersecurity Center of Excellence, a part of The National Institute of Standards and Technology (NIST), recently published a draft version of the Privileged Account Management for the Financial Services Sector report with new guidelines aimed to increase. ARCON Privileged Access Management Overview The nature of cyberattacks is getting sophisticated in the everexpanding digital workplace For enterprise IT security teams, protecting privileged accounts, one of the major sources of data breaches, remains a top priority Cyber attacks ca. Why is Privileged Account Management essential for every organization?.
Other privileged accounts which are often overlooked, but are just as vulnerable as the ones mentioned above, include service accounts, system accounts, application accounts, and SSH keys used by automated processes The modern approach to protecting these accounts is known as privileged access management or privileged access security (PAS). The NCCoE recently released a draft of the NIST Special Publication (SP) Privileged Account Management for the Financial Services Sector The project's public comment period closed on November 30, 18 For ease of use, the guide is available to download or read in volumes SP A Executive Summary. Privileged Access Management, also known as PAM, is a critical security control that enables organizations to simplify how they define, monitor, and manage privileged access across their IT systems, applications, and infrastructure Because administrator accounts have elevated privileges that can.
This lab is intended to show the basic features of the CyberArk Privileged Access Security solution (CyberArk PAS) CyberArk PAS is one of the leading solutions in the Privileged Account Management (PAM) space, which is what WWT considers one of the five pillars of Identity and Access Management. Automates discovery of privileged identities—privileged accounts, SSH keys, and SSL certificates Integrates with popular certificate authorities like DigiCert, GoDaddy, and Let's Encrypt out of the box, and helps achieve an endtoend life cycle management of SSL certificates and digital identities. Privileged user accounts are those to which rights to perform system and/or application administration have been assigned This policy defines the requirements surrounding the creation, use, monitoring, and decommissioning of privileged user accounts within the Franklin & Marshall data network.
Privileged Credential Risks Why Password Management is Needed Humanmanaged passwords With so many (constantly changing) passwords to remember, employees are prone to forget passwords, potentially locking them out of systemsTo compensate, they may apply the same passwords for multiple accounts, select easytoguess passwords, or resort to recording passwords on paper or within electronic. Privileged account management (PAM) is a part of identity and access management (IAM) that deals exclusively with the protection of privileged accounts in an enterprise, including those of operating systems, databases, servers, applications, virtual machines, and networking devices What is a privileged account?. The Password Server itself is a fullfeatured shared account and password management solution It can be used in combination with Remote Desktop Manager for privileged account and session management tools integrating over 150 integrations and technologies Download this Directory and get our Free Privileged Access Management Buyer’s Guide.
Privileged password management systems can periodically audit password records, monitor for account login sessions, trigger alerts, write to logs, and shut down suspicious activity effortlessly A privileged password manager should be able to help you formulate a password policy and should also have the utility to implement those decisions.

What Is Privileged Access Management Security Priority 1

Latest Stories Published On Best Privileged Account Management Articles Medium

What Is Privileged Access Management Onelogin
Privileged Account Management のギャラリー
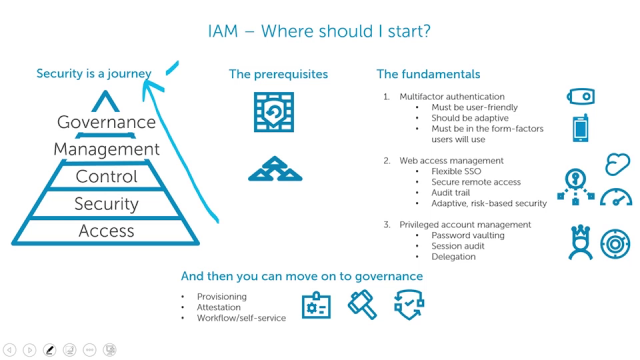
Learn Where To Start With Identity And Access Management

Privileged Account Management Jetzt Mit Multi Faktor Authentifizierung Von Yubikey Netzpalaver Cloudcomputing Datacenter Cybercrime Telekommunkation Infrastruktur

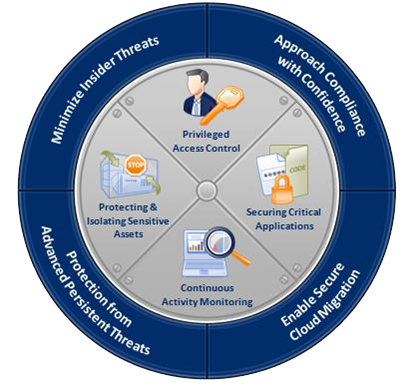
Shows How Privileged Access Management Pam Helps To Address Five Download Scientific Diagram

What Is Privileged Access Management Pam Read The Definition In Our Security Glossary Beyondtrust

Privileged Access Management Pam Solutions Ekran System

What Is Privileged Access Management Pam Varonis

Privileged Account Management 1 In Gartner Top 10 Security Projects
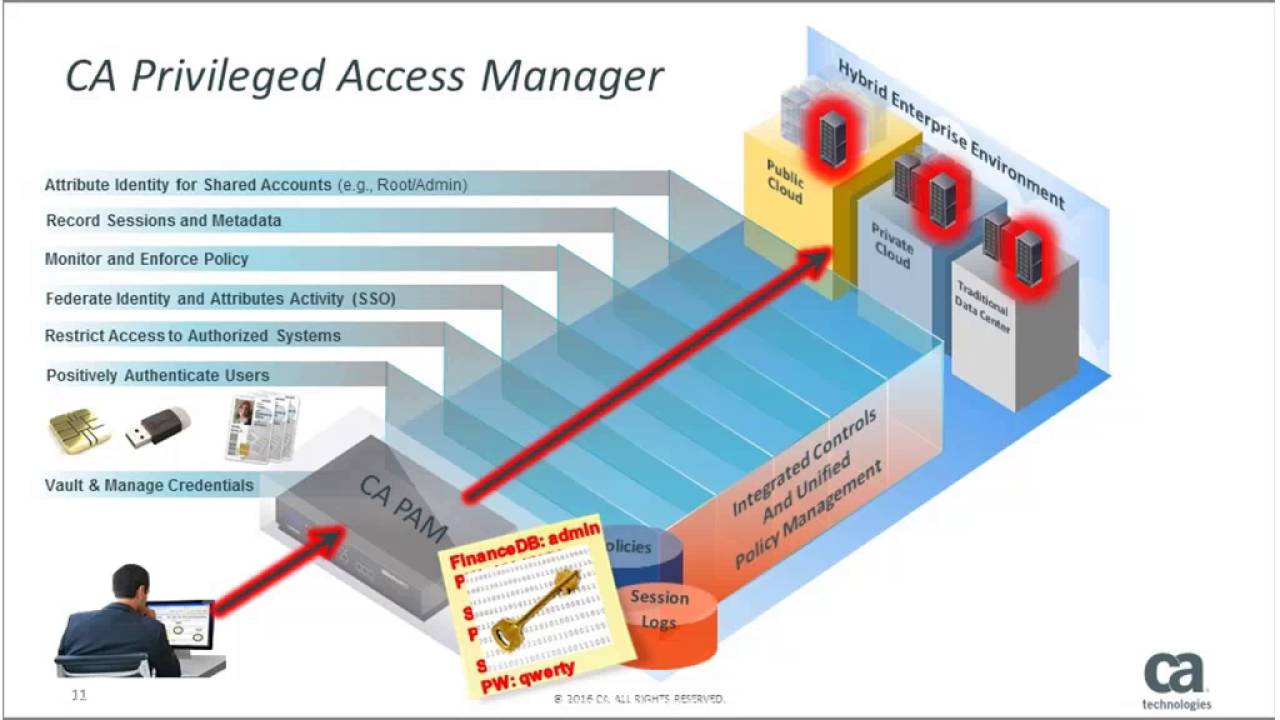
What Is Ca Privileged Access Manager Definition From Whatis Com

Why Privileged Access Management Is Essential For All Businesses Patecco En
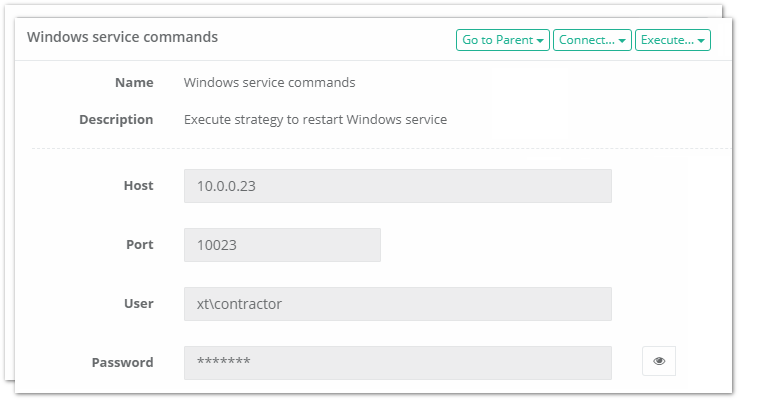
Privileged Access Management Pam Solutions Xton Technologies

How Privileged Account Manager Solves The Business Challenges Privileged Account Manager Administration Guide

What Is Privileged Access Management Security Priority 1
Http Wearearmadillo Com Wp Content Uploads 17 11 Cyberark Privileged Account Security Pdf
:quality(80)/images.vogel.de/vogelonline/bdb/1530700/1530793/original.jpg)
Pam Privileged Account Management
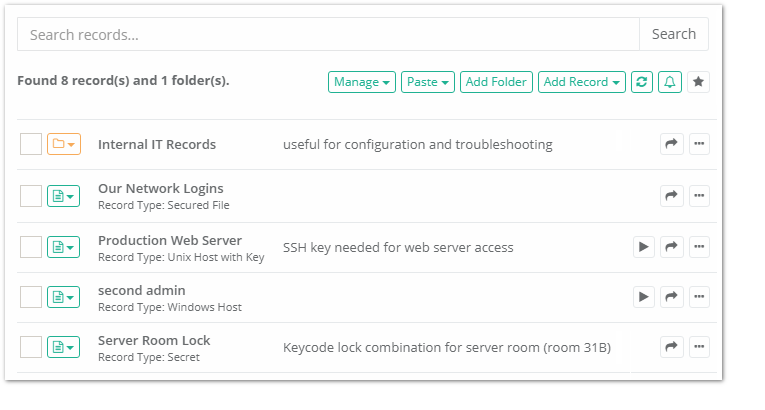
Privileged Access Management Pam Solutions Xton Technologies

Cyberark
Privileged Access Governance
Where To Begin A 7 Step Strategy To Achieving Complete Privileged Account Manag Beyondtrust
10 Steps To Better Windows Privileged Access Management
Privileged Account Manager

Privileged Access Management Netiq Privileged Account Manager Micro Focus
Tech Talk Privileged Account Management Maturity Model

Powerful Privileged Access Management Cloud Or On Premises

10 Features Every Privileged Access Management Solution Must Have Security Boulevard

Privileged Account Management Tool Sicherheitsuberwachung Solarwinds
Q Tbn And9gcra3bbhof R0q9celbr14idqicmddrf9hwgenqk1a Bl D9qcom Usqp Cau
Privileged Access Management Okta

Privileged Account Management 101 How Can Privileged Accounts Compromise Your Security
Cyberark Privileged Account Management Infoguard

Pam Deployment Is Challenging And Requires Well Managed Projects

Privileged Access Management For Active Directory Domain Services Microsoft Docs

What Is Privileged Account Management Pam

Enterprise Secrets Privileged Account Management Cyberark At Xfd1 Wilson Tech

Privilege Account Management Solidfish
Gedanken Zum Privileged Identity Management Und Privileged Account Management
Fur Privileged Accounts Ein Absolutes Muss Zugriffskontrolle Uberwachung Und Reaktionsmoglichkeit It Daily Net

Privileged Identity Management
1
Www Nccoe Nist Gov Sites Default Files Library Project Descriptions Fs Pam Project Description Draft Pdf

Why Privileged Access Management Pam Should Be Cisos Top Priority

Cst Thycotic Privileged Account Management For Dummies
Infographics Ten Functions Of Privileged Account Management Xton Technologies

How To Manage Privileged Accounts And Identities Micro Focus Community

Secret Vault Privileged Account Management Platin Bilisim

Application Model For Privileged Account Access Control System In Enterprise Networks Sciencedirect

What Is Privileged Account Management Manageengine Password Manager Pro
Tech Talk Privileged Account Management Maturity Model

Pam Privileged Account Management

Can Privileged Account Management Really Stop Credential Theft Javelin Networks Blog

Privileged Access Management In Office 365 Is Now Generally Available Microsoft Tech Community
Privileged Account Management 101 How Can Privileged Accounts Compromise Your Security

Privileged Account Management Econet

What Is Privileged Account Management Pam

Privileged Access Threat Report 19 Beyondtrust
The Seven Keys To A Successful Privileged Account Management Strategy Kuppingercole
7 Essential Features Of A Perfect Privileged Access Management Solution

Privileged Access Management Pam Is The 1 Cyber Security Priority

Privileged Access Management For Active Directory Domain Services Microsoft Docs

Privilege Account Lifecycle Management Arcon Blog

3 Strategic Decisions That Power Your Privileged Account Access Approach Cybersheath

19 Zero Trust Privilege Maturity Model Episode 1

Ciso Series Secure Your Privileged Administrative Accounts With A Phased Roadmap Microsoft Security

Pam Market Size Worldwide Statista
Privilege Access Management

Managing The Keys To The Kingdom Privileged Shared Accounts Simeio Solutions Oracle Cloud Security Blog
Privileged Account Management 101 How Can Privileged Accounts Compromise Your Security
Privileged Account Management Best Practices

The Security Sector To Watch Privileged Account Management By Jeffrey Feng Medium

One Identity Manager Privileged Account Governance 3 Safeguard User Management Youtube
Q Tbn And9gcrnc1smthjizbbj9kds2igecehsrafcgcyawyjytan2vuxatk Usqp Cau
Understanding Oracle Privileged Account Manager
Cyberark Privileged Account Management Wwt

Privileged Account Management Tool Sicherheitsuberwachung Solarwinds
:quality(80)/images.vogel.de/vogelonline/bdb/1530700/1530794/original.jpg)
Pam Privileged Account Management
Privileged Account Management A Mandatory Requirement A Dnext
Password Life Cycle Password Safe Passwortverwaltung

Protect Your Matrix With Strong Privileged Access Management
Privileged Account Management Is Critical For Information Security
What Is Privileged Access Management Pam Read The Definition In Our Security Glossary Beyondtrust
B2bsalescafe Files Wordpress Com 17 11 Market Guide For Privileged Access Management Aug 17 Pdf

Privileged People And Powerful Systems Balancing Trust With Thycotic Techhq

What Is Privileged Access Management Pam Varonis

What Is Privileged Access Management Core Security

Learn About Privileged Access Management Microsoft 365 Compliance Microsoft Docs
Wer War Root Was Sie Uber Privileged Account Management Pam Wissen Sollten Kuppingercole

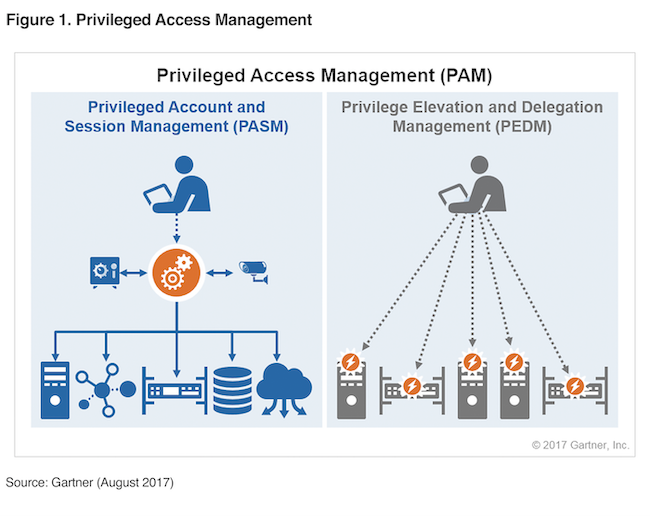
Different Paths Same Goal Privileged Account And Session Management Pasm And Privilege Elevation And Delegation Management Pedm

Implementing Privileged Access Management Pam The Pam Lifecycle

What Is Privileged Account Management Manageengine Password Manager Pro
Gedanken Zum Privileged Identity Management Und Privileged Account Management

What Is Privileged Access Management Pam Varonis

How Privileged Account Manager Solves The Business Challenges Privileged Account Manager Administration Guide

7 Most Common Privileged User Management Systems The Techeries

Cyberark Privileged Account Management Infoguard

What Is Privileged Access Management Pam Explained Security Wiki
Q Tbn And9gcrnc1smthjizbbj9kds2igecehsrafcgcyawyjytan2vuxatk Usqp Cau

Top 5 Poor Privileged Account Management Practices Ekran System
The Components Of Privileged Account Management Process Download Scientific Diagram
Privileged Password Management Solution Privileged User Account Manager
Privileged Access Management Solutions Overview

Top Best Privileged Account And Session Management Vendors Solutions 19 Youtube

Breaches Are Inevitable Adding Resiliency To Your Pam Program Technology Insights Blog



