Security Incident Management
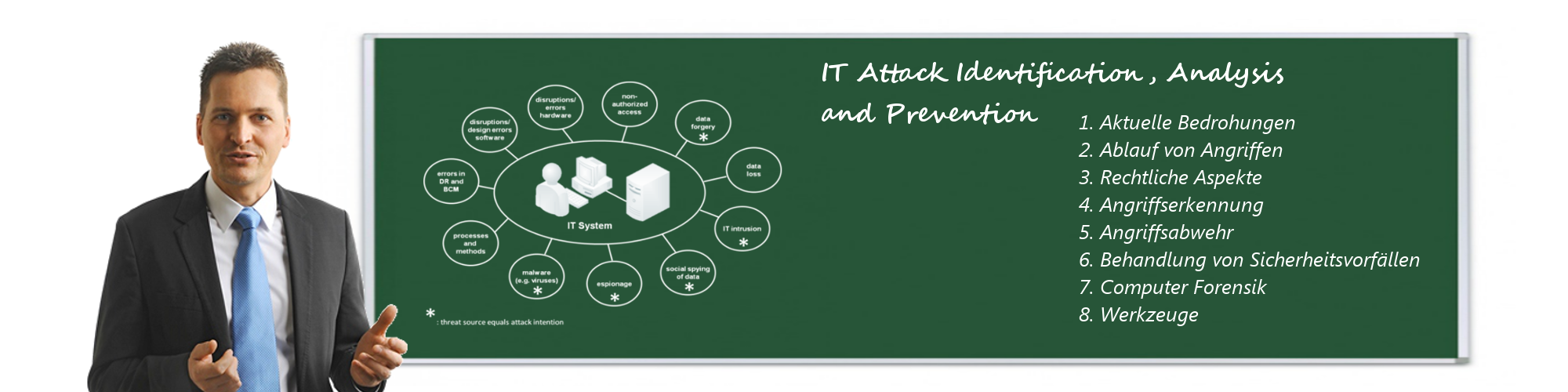
Computer security incident management is a specialized form of incident management, the primary purpose of which is the development of a well understood and predictable response to damaging events and computer intrusions Incident management requires a process and a response team which follows this process.

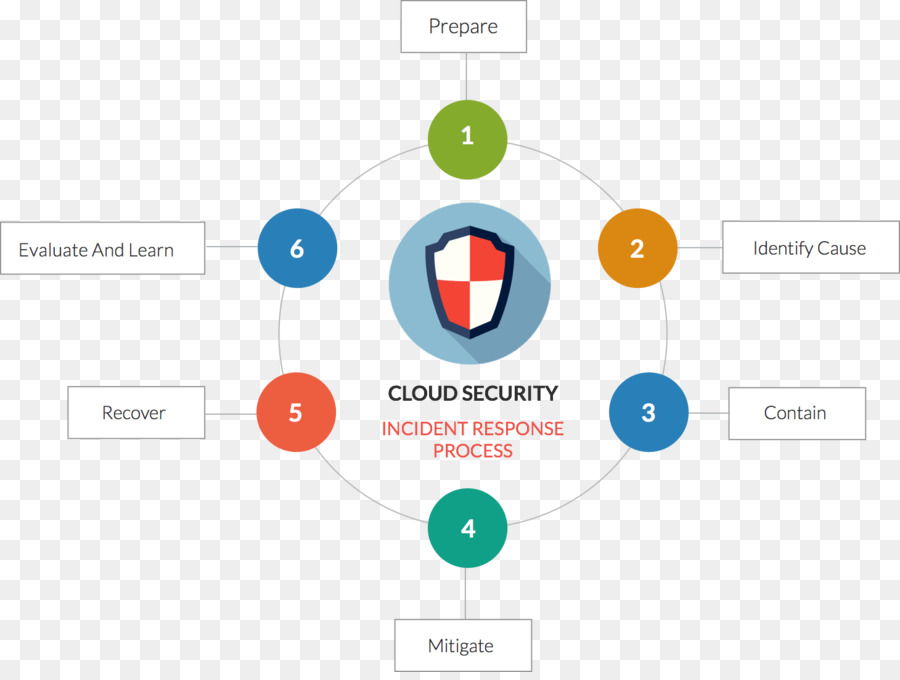
Security incident management. The National Incident Management System (NIMS) guides all levels of government, nongovernmental organizations and the private sector to work together to prevent, protect against, mitigate, respond to and recover from incidents NIMS provides stakeholders across the whole community with the shared vocabulary, systems and processes to successfully deliver the capabilities described in the. What is an incident response plan for cyber security?. Learn how to manage a data breach with the 6 phases in the incident response plan An incident response plan is a documented, written plan with 6 distinct phases that helps IT professionals and staff recognize and deal with a cybersecurity incident like a data breach or cyber attack.
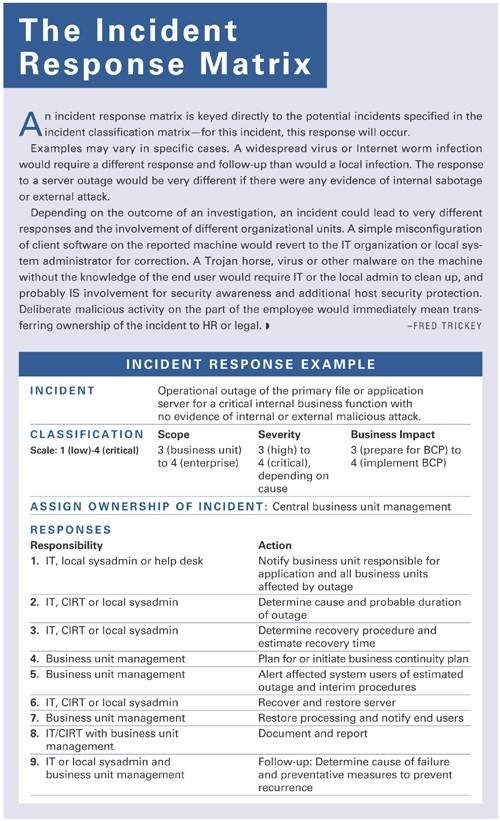
Their major responsibilities include taking responsibility for overall incident management and response concept, approving incident management team charter, approving exceptions or deviations, and making the final decisions • The information security manager is the incident management team leader and is the main interlace to SSG. Incident Management involves returning your organization’s everyday business safety, productivity, and overall operation, to normal as quickly as possible after an incident Topics such as principles of incident management, incident management methodology, and incident typology will be covered in detail. Computer security incident response has become an important component of information technology (IT) programs Because performing incident response effectively is a complex undertaking, establishing a successful incident response capability requires substantial planning and resources This publication assists organizations in establishing computer security incident response capabilities and.
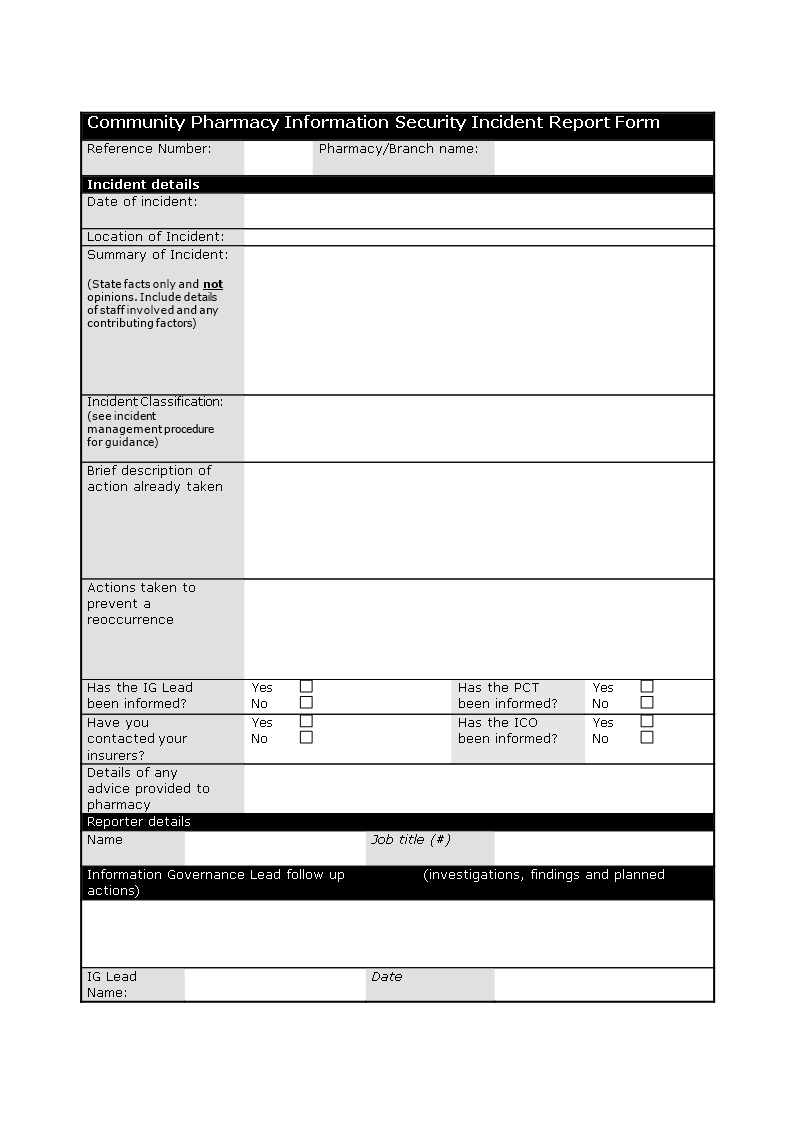
Information Security Incident Response Procedure v13 Page 8 of 16 may be escalated or deescalated by the information security staff for an electronic incident All incident reports are to be made as soon as possible after the incident is identified, and with minimum delay for medium to high severity incidents. Incident response plan (IRP) An incident response plan (IRP) is a set of written instructions for detecting, responding to and limiting the effects of an information security event. Whatever your risk assessment method looks like, one thing is certain – securityrelated incidents should be handled by Incident Management (or, in ISO 000, Incident and Service Request Management) Use this article Incident Management in ITIL – solid foundations of operational processes to learn more about the Incident Management.
Incident response plan (IRP) An incident response plan (IRP) is a set of written instructions for detecting, responding to and limiting the effects of an information security event. The ServiceNow® Security Incident Response application tracks the progress of security incidents from discovery and initial analysis, through containment, eradication, and recovery, and into the final post incident review, knowledge base article creation, and closure Request apps on the Store Visit the ServiceNow Store website to view all the available apps and for information about. The Security Incident Management dashboard presents the following key performance indicators New Security Incidents A chart of the number of new security incidents.
Computer security incident response has become an important component of information technology (IT) programs Because performing incident response effectively is a complex undertaking, establishing a successful incident response capability requires substantial planning and resources This publication assists organizations in establishing computer security incident response capabilities and. A security incident is a specific incident type indicating that the organization’s systems or data have been compromised A data breach is a confirmed security incident in which sensitive, confidential or otherwise protected data has been accessed and/or disclosed in an unauthorized fashion. A powerful and pragmatic approach to security incident management, meeting Annex A16 of ISO , and the requirements of GDPR See how simple it is with ISMSonline Book a demo fabolt Managing security incidents couldn’t be simpler.
Ensure that there are written incident response plans that defines roles of personnel as well as phases of incident handling/management Assemble and maintain information on thirdparty contact information to be used to report a security incident, such as Law Enforcement, relevant government departments, vendors, and ISAC partners. A security incident refers to any unlawful access to customer data stored on Microsoft’s equipment or in Microsoft’s facilities, or unauthorized access to such equipment or facilities that has the potential to result in the loss, disclosure, or alteration of customer data. Incident response plan (IRP) An incident response plan (IRP) is a set of written instructions for detecting, responding to and limiting the effects of an information security event.
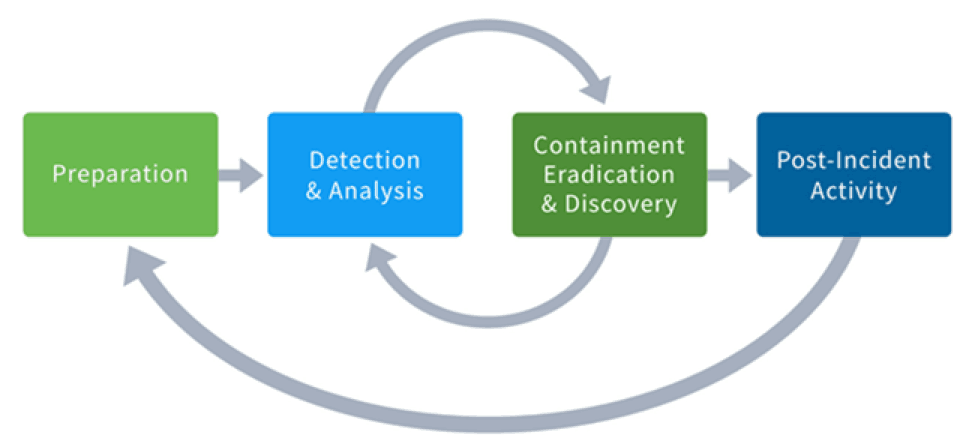
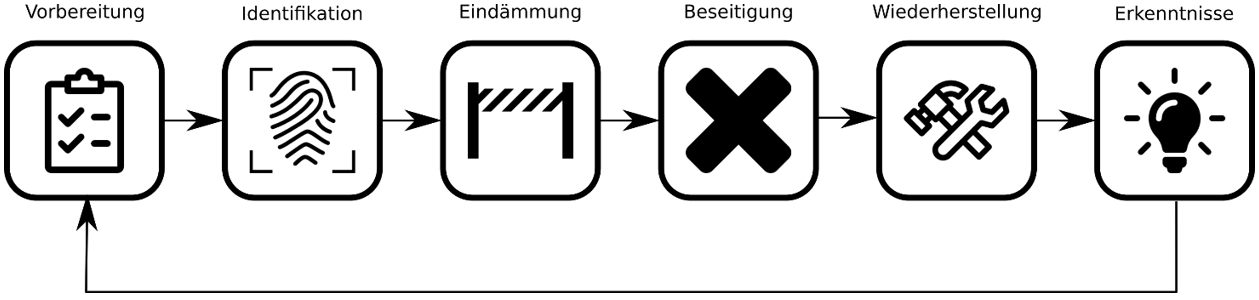
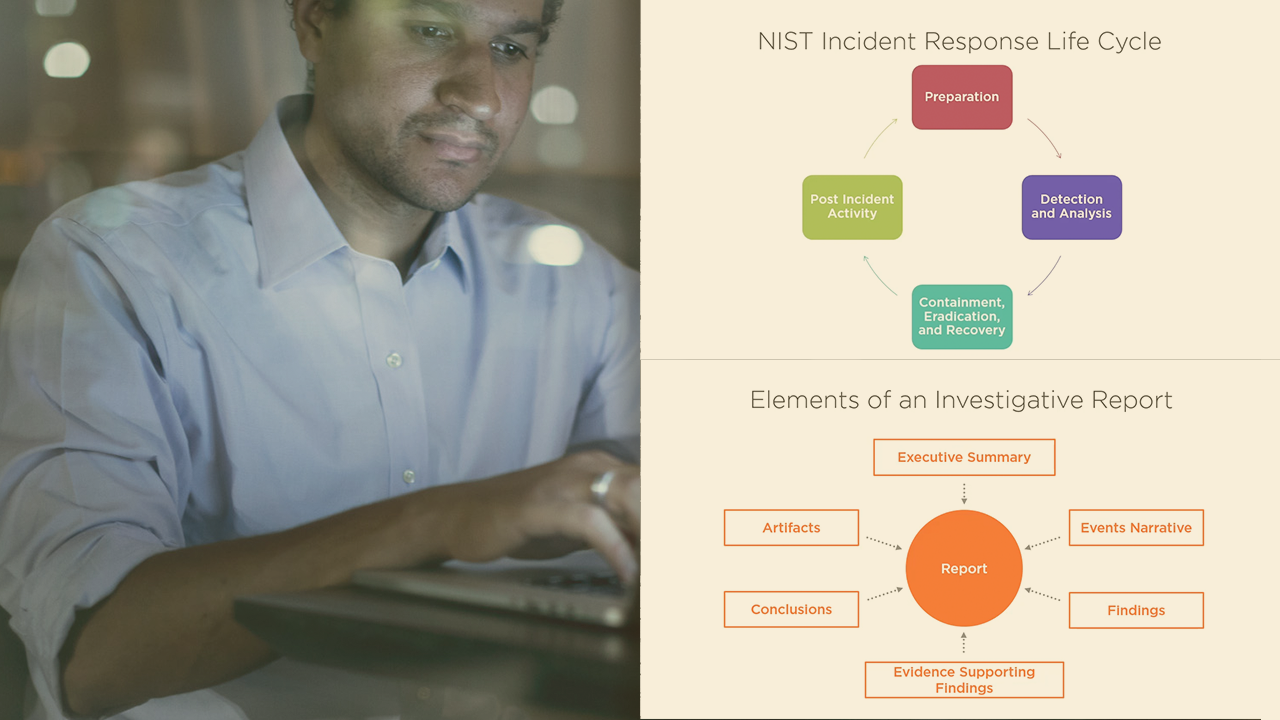
By the time IT professionals have thoroughly researched a potential threat, it may have already escalated into something more serious Remove the manual research involved in incident response and let the security incident management software in Security Event Manager with Active Response do the heavy lifting. It’s a cycle that consists of a preparation phase, an incident detection phase and a phase of incident containment, mitigation and recovery The final phase consists of drawing lessons from the incident in order to. This process of identifying, analyzing, and determining an organizational response to computer security incidents is called incident management1 The staff, resources, and infrastructure used to perform this function makeup the incident management capabilityHaving an effective incident management capability in place is an important part of the.
The Security Incident Management Tool provided within ISMSonline will make information security incident management a simple, effortless task for you as it guides an incident through the key states, thus ensuring the standard is being met in a pragmatic yet compliance fashion. The Cherwell Information Security Management Solution (ISMS) is designed based on a proven NIST framework for security incident response and remediation that allows organizations to handle incidents efficiently and effectively, as well as associate risk and incidents to change and ensure security co. Security Incident and Event Management (SIEM—pronounced as SIM or SEEM) is a security management approach, which combines functions of Security Information Management (SIM) and Security Event Management (SEM) to define a sound security management system While SIM focuses on automating the collection of log data, events, and flows from.
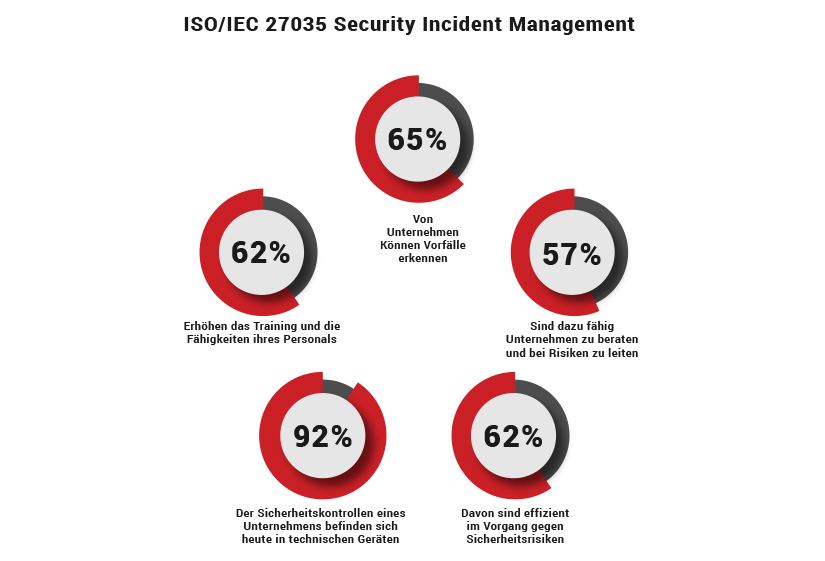
Determine which security events, and at what thresholds, these events should be investigated Then create an incident response plan for each type of incident It can be improved through security event simulations, where you identify holes in your process, but it will also be improved after actual events (more on that later). Security incident management is a critical control by ISO standards (Clause A13), and has an equal, if not higher, level of importance in other standards and frameworks incident management. AlienVault USM is a comprehensive tool combining threat detection, incident response, as well as the compliance management to provide comprehensive security monitoring and remediation for onpremise and cloud environments The tool has multiple security capabilities that also include intrusion detection, vulnerability assessment, asset.
Any incident responder worth their salt knows what a Security Information and Event Management system is, so this question should be a nobrainer if it comes up in the interview All a SIEM does is aggregate data from multiple sources and compile them into meaningful information. Learn how to manage a data breach with the 6 phases in the incident response plan An incident response plan is a documented, written plan with 6 distinct phases that helps IT professionals and staff recognize and deal with a cybersecurity incident like a data breach or cyber attack. What is an incident response plan for cyber security?.
Information Security Management Act (FISMA), Public Law (PL) NIST is responsible for Computer security incident response has become an important component of information technology (IT) programs Because performing incident response effectively is a complex undertaking, establishing a. A Computer Science portal for geeks It contains well written, well thought and well explained computer science and programming articles, quizzes and practice/competitive programming/company interview Questions. In any security incident, the stakeholders are the key positions who are affected the most, based on the type of incident and the particular assets that were targeted The organization has lots of resources to be targeted, as the stakeholders include various internal public like management, partners, departments, etc.
An institution's information security incident response management program is evidenced by policies and incident handling procedures These documents should be clear and concise, describing the steps all campus members (from end user to incident response staff to leadership) must take in response to an actual or suspected incident. 1 Policy Statement Incident Management policy shall enable response to a major incident or disaster by implementing a plan to restore the critical business functions of XXX The number of computer security incidents and the resulting cost of business disruption and service restoration rise with increase in dependence on ITenabled processes. A Computer Science portal for geeks It contains well written, well thought and well explained computer science and programming articles, quizzes and practice/competitive programming/company interview Questions.
< Previous standard ^ Up a level ^ Next standard > ISO/IEC — Information technology — Security techniques — Information security incident management (parts 1 3 published) Introduction Information security controls are imperfect in various ways controls can be overwhelmed or undermined (eg by competent hackers, fraudsters or malware), fail in service (eg authentication. Security Incident Management and the CMS’ Emergency Preparedness Plan In addition to the unique challenges faced by each healthcare facility, those in receipt of payments from the Centers for Medicare and Medicaid Services (CMS) also have to comply with the CMS’ Emergency Preparedness Plan The objective of the Emergency Preparedness Plan. The key for IT security managers thinking about or planning for incident management is to understand the objective of incident handling as an independent "project".
11 Security Incident Management Process Objective The objective of the Security Incident Management (SIM) process is to remediate security incidents and breaches, and ensure secure operations, in accordance with contractual and securityrelated legal requirements Process Description All SAP employees, contractors, and thirdparty users of information systems and services are required to. A Computer Science portal for geeks It contains well written, well thought and well explained computer science and programming articles, quizzes and practice/competitive programming/company interview Questions. Security Incident Response Management Minimize Impact of Security Events As cyberattacks become more common, organizations need to be prepared to efficiently manage the increasing volume and severity of security events and incidents The Cherwell Security Management solution is designed based on a proven NIST framework for security incident.
Incident management is therefore the process of limiting the potential disruption caused by such an event, followed by a return to business as usual Without effective incident management, an incident can disrupt business operations, information security, IT systems, employees, customers, or other vital business functions. Explain how Microsoft defines a Security Incident, the federated model that Microsoft uses for Security Incident Response across the organization, and how customers and Microsoft share responsibility for security in the cloud Describe how Microsoft prepares to deal with security issues through training, testing, and knowledge sharing. A Computer Science portal for geeks It contains well written, well thought and well explained computer science and programming articles, quizzes and practice/competitive programming/company interview Questions.
There are three cardinal truths of incident management The first is that incidents are inevitable—especially for companies that are constantly growing and innovating The second is that a strong incident management practice is vital to a healthy business (and a weak one costs businesses big in both employee time and satisfaction and business revenues). Cyber security incident management is not a linear process;. In IT, a security event is anything that has significance for system hardware or software, and an incident is an event that disrupts normal operations.
Security incident management is the process of identifying, assessing, and managing threats to a company’s IT infrastructure, both electronic and physical More specifically, information security issues are not limited to data breaches and can include issues such as a lost or stolen laptop, web application security issues, and attempted. The key for IT security managers thinking about or planning for incident management is to understand the objective of incident handling as an independent "project". The primary elements of incident management are Effective incident response in many organizations other than IT, involve having trained personnel equipped and ready for response So it is with information security incident management Having trained individuals ready to respond with advance preparation is the first task.
Information Security Incident Management at NASA is a lifecycle approach, represented by Figure 1 – The Incident Management Lifecycle, and is composed of serial phases (Preparation, Identification, Containment, Eradication, Recovery, and Follow‐Up) and of. Ineffective incident management may result in a greater loss of or longer disruption to business operations or services, adversely impacting information security, information systems, employees, customers, or other critical business functions of the service organization. Download Security Incident Management in Microsoft Office 365 from Official Microsoft Download Center Microsoft 365 Premium Office apps, extra cloud storage, advanced security, and more—all in one convenient subscription For up to 6 people For 1 person Power BI.
Incident management capabilities that are institutionalized as CSIRTs or security teams often face the hurdles of having to justify the need for their existence, gaining that support and understanding for the problems they are trying to address, and getting key management buyin Organizations such as the Government Forum of Incident Response.

Cyber Security Incident Response Cheat Sheet Cyber Security Behavior Analysis Analysis
Security Incident Management Archives Sure It

Developing Hands On Laboratory Works For The Information Security Incident Management Discipline Springerprofessional De
Security Incident Management のギャラリー

What Is Security Incident Management The Cybersecurity Incident Management Process Examples Best Practices And More Digital Guardian

Digital Arbeiten Heisst Vielfaltig Arbeiten Axians Ict Austria

The Complete Information Security Incident Management Process Download Scientific Diagram

Computer Security Incident Management Incident Response Team Computer Emergency Response Team Png 908x841px Incident Management Brand
Leitfaden Zur Bildung Einer It Security Incident Response Strategie 978 3 639 361 4 By Horst Rockelein

Behind The Scenes Of Our Security Incident Management Process Work Life By Atlassian
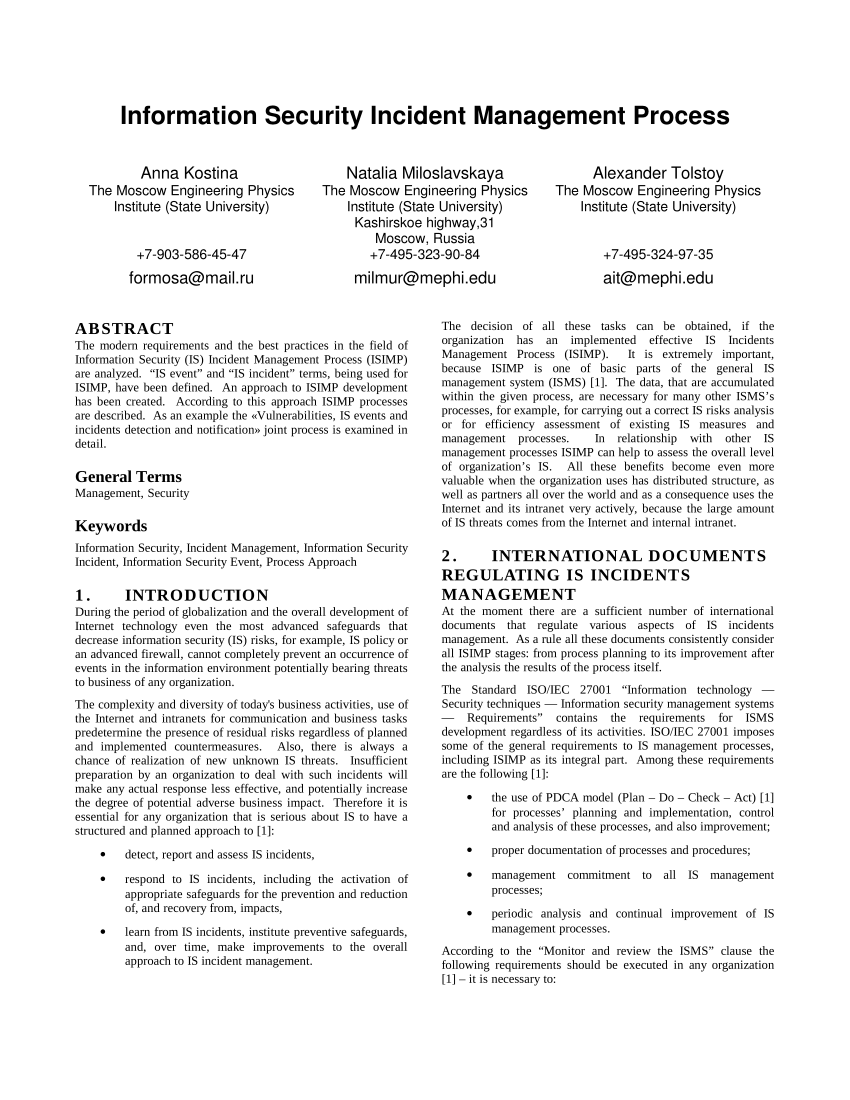
Pdf Information Security Incident Management Process

Top 5 Incident Management Issues

How To Create A Security Incident Management Standard For Your It Organization Download T In Management Information And Communications Technology Risk Management

Computer Security Incident Management Wikipedia
Security Comscore Inc

Incident Response Policy An Overview Sciencedirect Topics
Cloud Computing Security Schaltplan Computer Security Incident Management Cloud Computing Png Herunterladen 1460 1090 Kostenlos Transparent Text Png Herunterladen

Iso A 16 How To Handle Security Incidents

Pecb Infographic Information Security Incident Response Process Mode

Iso Iec 16 Information Technology Security Techniques And Information Security Incident Management Argus Cyber Security

Security Incident Management Should Feed Into Risk Management Jsec Se

A Readiness Model For Measuring The Maturity Of Cyber Security Incident Management Springerprofessional De
All Incidents Aren T The Same Time For Your Security Incident Management Plan Ivanti
Www Bfh Ch Dam Jcr 993b861e 944b 4e94 41 de Study Guide Cas Security Incident Management Pdf

Security Incident Management On Servicenow Express Youtube
The Cio S Guide To Information Security Incident Management Pemble Matthew William Arthur Goucher Amazon De Bucher
Pdf Information Security Incident Management Identified Practice In Large Organizations

Figure 1 From Computer Security Incident Response Team Development And Evolution Semantic Scholar

Fir Fast Incident Response Cyber Security Incident Management Platform Darknet

Sicherheits Incident Management Cyber Incident Behandlung Rsa Archer

Computer Security Incident Management Computer Software Arcsight D3 Sicherheits Management Systeme Untersuchung Png Herunterladen 2114 1408 Kostenlos Transparent Computer Symbol Png Herunterladen

Cyber Security Incident Response Plan Template Unique Incident Management Process Flow Google Search Management Cyber Security Business Process Management

31 Iso 13 A16 Is Incident Management Youtube

Cyber Security Incident Management Guide

Develop And Implement A Security Incident Management Program
Computer Security Incident Management Wikipedia
A Readiness Model For Measuring The Maturity Of Cyber Security Incident Management Springerlink

Pdf Information Security Incident Management Process Semantic Scholar

Iso A 16 How To Handle Security Incidents

Thehive Security Incident Response Platform Sectechno

Cas In It Security Incident Management An Der Bfh Do It Swiss

A Survey Of Information Security Incident Handling In The Cloud Sciencedirect

Information Security Incident Management Process

Computer Security Incident Management Computer Emergency Response Team Organisation Raumung Png Herunterladen Kostenlos Transparent Text Png Herunterladen

Sicherheits Incident Management Cyber Incident Behandlung Rsa Archer

Security Incident Management Iso Isms Wmc
Business Continuity Roles Improve Security Incident Management

Understanding Security Incident Response Servicenow Docs

Cyber Security Incident Response

Security Incident Management Iso Isms Wmc

Security Incident Management In Microsoft Dynamics 365

Word Writing Text Computer Security Incident Management Business Concept For Safe Cyber Technology Analysisaging Magnifying Glass Over Chosen Man Figure Among The Hu Analysis Dummies Line Up Lizenzfreie Fotos Bilder Und Stock

Organisation Computer Security Incident Management Incident Response Team Incident Management Png Herunterladen 601 600 Kostenlos Transparent Text Png Herunterladen
Iso Training Examination Audit And Certification Pecb

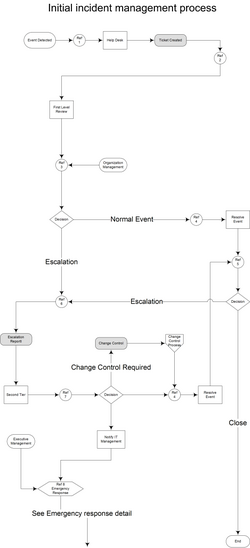
Security Incident Management Process Download Scientific Diagram
Cyber Security Incident Response Accelerate Digital Innovation

The Overlooked Importance Of Incident Management Dflabs
Open Platform And Tools To Facilitate The Collaboration Among Computer Security Incident Response Teams Enisa
Cyber Security Incident Response Accelerate Digital Innovation

Security Incident Management Iso Isms Wmc

Process Street
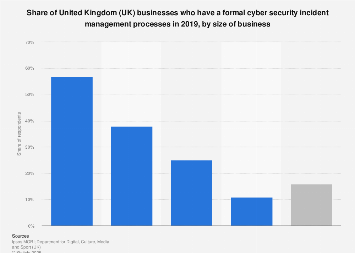
Uk Businesses Cyber Security Incident Management Processes 19 Statista

Chapter 15 Information Security Incident Management Infosec Management Fundamentals Book

Engineering Cartoon Png Download 491 536 Free Transparent Computer Security Incident Management Png Download Cleanpng Kisspng

Security Incident Management Process Download Scientific Diagram
6 Incident Response Steps To Take After A Security Event

Actionable Cyber Security Incident Management Swiss Cyber Forum

Incident Management Infographic Siem By Hari Harann Medium

Security Incident Management Using 4me Youtube

Risk Security Intelligence Team Radar Cyber Security
Cyber Security Incident Response So Bewaltigen Sie Das Unerwartete Oneconsult Ag
Security Incident Response Approach Download Scientific Diagram

Eine Einfuhrung In Das Cyber Security Incident Response Management Und Best Practices
Kostenloses Information Security Incident Report Template
Incident Handling And Response A Holistic Approach For An Efficient Security Incident Management Amazon De Alex Jithin Fremdsprachige Bucher
Www Kbv De Media Sp Kbv Snk Rlex Sim V1 0 Pdf

Workflow For Cyber Security Incident Response Team Implemented In Download Scientific Diagram
The Cio S Guide To Information Security Incident Management Pemble Matthew William Arthur Goucher Amazon De Bucher

Security Operations Management Risiken Und Kosten Reduzieren Axios Systems
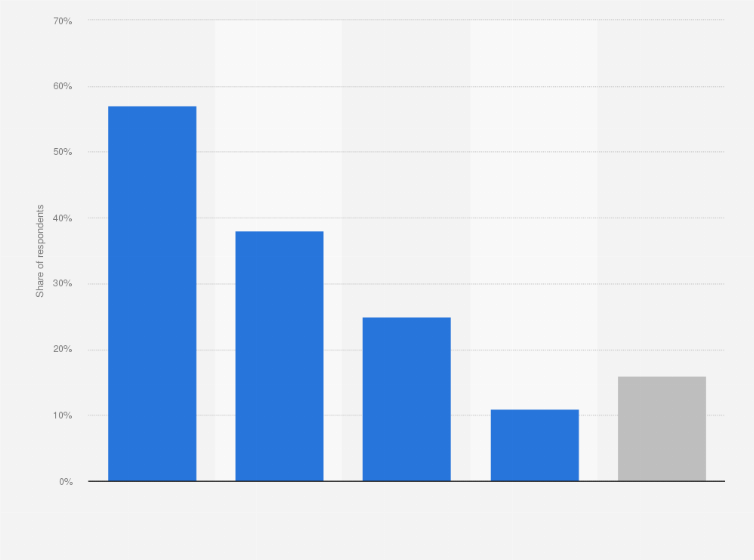
Uk Businesses Cyber Security Incident Management Processes 19 Statista

Cyber Security Incident Response Some Valuable Lessons Learned Cyber Security It Service Provider Prevention
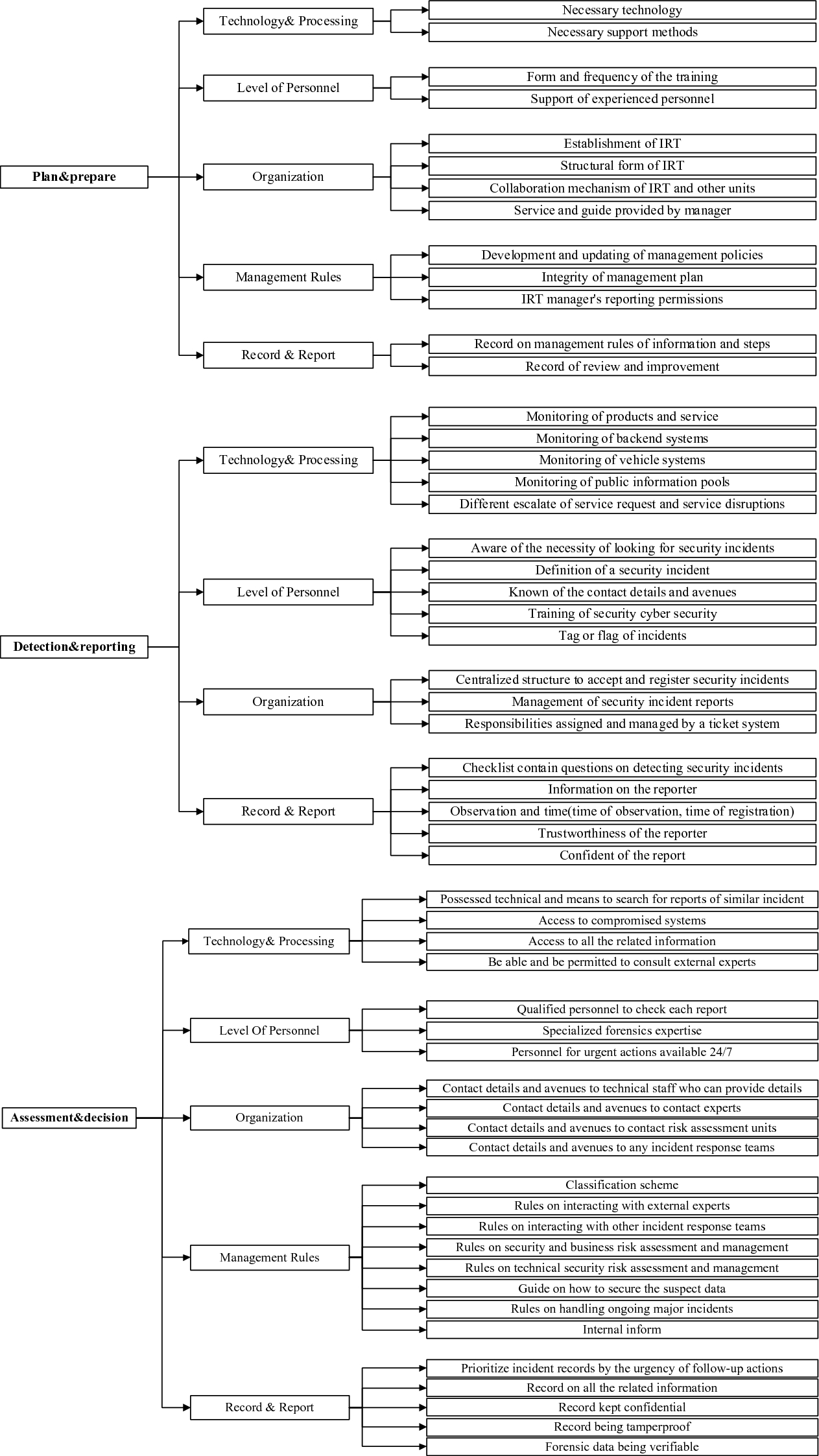
Study On Incident Response System Of Automotive Cybersecurity Springerlink
A Readiness Model For Measuring The Maturity Of Cyber Security Incident Management Springerlink

Computer Security Incident Response Plan Management Itom Marketplace

Infra Provisioning Evolution Computer Security Incident Management Free Transparent Png Download Pngkey

Pdf Best Practices For Establishment Of A National Information Security Incident Management Capability Isimc

Security Incident Management Pilz Int

Cyber Security Incident Response Konzeptacht Gmbh
Handlungsempfehlung Zum Aufbau Eines Security Incident Management Pdf Free Download

Computersicherheits Storungsmanagement Ursachenanalyse Computer Notfallteam Incident Management Png Herunterladen 1000 667 Kostenlos Transparent Text Png Herunterladen

Security Incident Management Leitfaden Fur Kraftwerksbetreiber Security Incident Management German Edition By Amazon Ae
Security Incident Management Leitfaden Fur Kraftwerksbetreiber 978 6 2 1 By Julian Obenland
About Hirt Hitachi Incident Response Team Hitachi

The Process That Itil Forgot Security Incident Response

Strukturierte Planung Einer Incident Response Readiness

Sicheres Netz Der Kven Richtlinie Security Incident Management Pdf Kostenfreier Download

Security Incident Response Threat Intelligence Servicenow
Information Security Manager Information Security Incident Management Pluralsight

Incident Management Assessment Fujitsu Deutschland

Bpmn Model Of The Security Incident Management Process Simp Download Scientific Diagram
Handlungsempfehlung Zum Aufbau Eines Security Incident Management Pdf Free Download



